How to Store Private key and Mnemonic on Google Cloud
If you are developing dApps or Web3 protocols, chances you’ll need to store private key or mnemonic of protocol’s hot wallet on server. However, storing private key as plain text is very unsecure. Setting up encryption or key manager is recommended. Luckily, if you’re using Google Cloud Function or Cloud Run for your service, you can use Google secret manger to store private keys or mnemonic safely.
Setting Up Secret
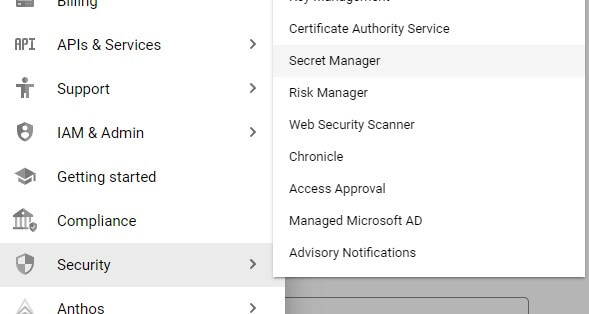
First, we’ll need to setup a secret. On Google Cloud Console, go to “Security” and “Secret Manager” (You will need to enable Google Cloud Secret API first)
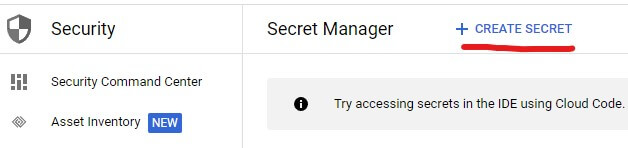
Click “Create Secret”
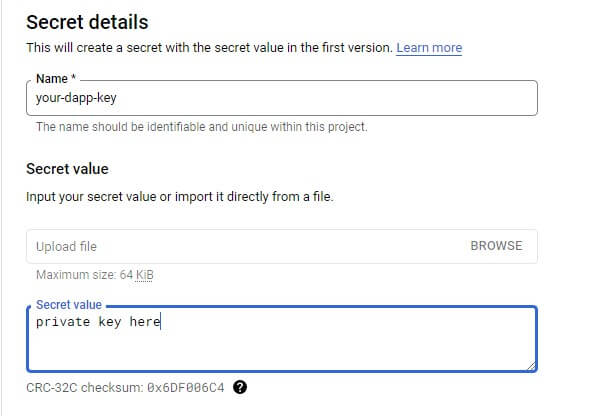
Name your secret and put the mnemonic or private key in secret value
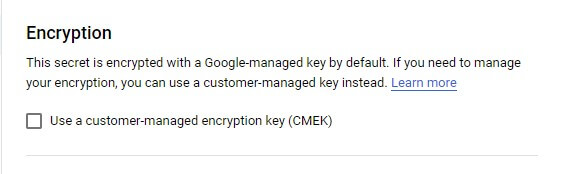
Normally secret will be encrypted by Google but you can manage your own encryption
Once completed, you will see your secret under the secret manager
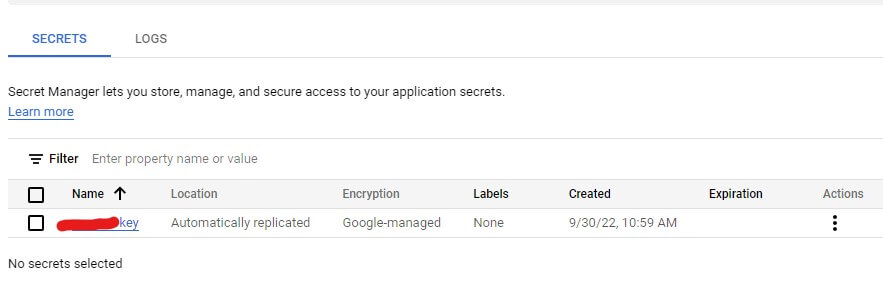
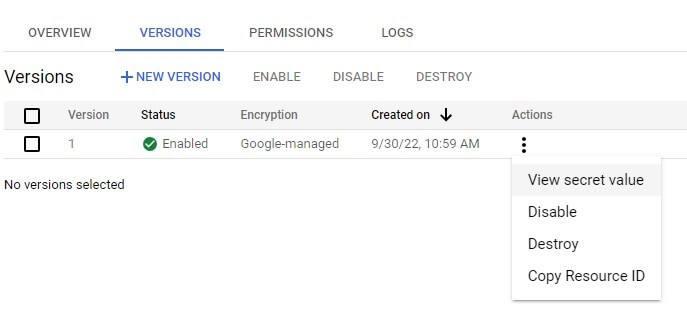
You can have multiple version of the secret. To view secret value, you will need to click the required version and select “View secret value”
Accessing the Key
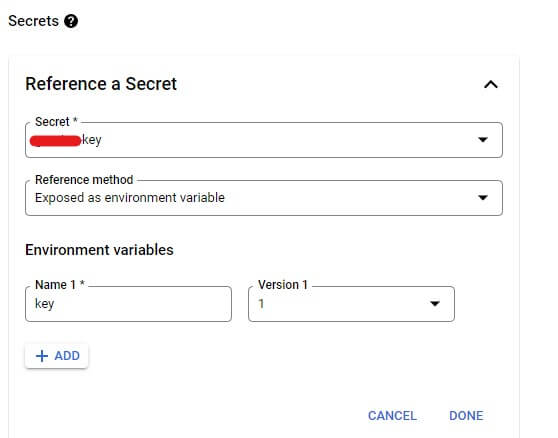
Your Google Cloud Run or Function can access secret as an environment variable or mounted drive. You’ll need to select the secret and reference method under “Secrets” section setting.
For example, you can access secret via environment variable in node.js like this.
var mnemonic = process.env.YOUR_SECRET_KEY_NAME;

